The new financial system is already here.
But access alone isn’t enough.
If you don’t secure it properly, the system will not protect you—
and no one is coming to fix it after the fact.
This is not banking.
This is ownership.
And ownership comes with responsibility.
The Wallet Is Control — Not Convenience
A wallet gives you:
- Direct ownership
- Permissionless access
- Full responsibility
There is no fraud department.
No password reset button.
No reversal.
If you lose access, it’s gone.
That is the trade.
Hot vs Cold Wallets (You Need Both — But Used Correctly)
Hot Wallets (Connected to the Internet)
Used for:
- Transactions
- Apps, DeFi, gaming
- Daily movement of funds
Examples:
- MetaMask
- Trust Wallet
Risk reality:
Anything connected to the internet is exposed.
Hot wallets are tools—not vaults.
Cold Wallets (Offline Storage)
Used for:
- Long-term holdings
- Wealth protection
- Storage outside online risk
Examples:
- Ledger Nano X
- Trezor Model T
Reality:
Cold wallets are your vault.
If you’re serious, this is where your assets belong.
The Real Threats (What Actually Causes Loss)
Forget the headlines. Most losses come from:
- Phishing links
- Fake apps or browser extensions
- Poor password habits
- Storing recovery phrases digitally
- Reusing emails across platforms
- Blindly signing transactions
Not hacking.
Carelessness.
Your Security Stack (Non-Negotiable)
If you’re going to operate in this system, you build layers.
Not one point of failure.
1. Hardware Wallet (Cold Storage Layer)
- Stores your private keys offline
- Never exposes them to the internet
- Used for long-term holdings
Rule: Large value never sits in a hot wallet.
2. Separate Hot Wallet (Operational Layer)
- Used for daily activity
- Connected to apps and services
Rule: Only keep what you’re willing to risk.
3. Dedicated Email (Identity Layer)
Create a clean email used only for crypto.
- No social media
- No random signups
- No reuse
Why: Most attacks start with email access.
4. Strong Password System
- Unique password for every account
- Minimum 16+ characters
- Stored in a password manager (not your head, not a notebook on your desk)
Reality: Reused passwords are how people get wiped out.
5. 2FA (But Done Correctly)
Use:
- Authenticator apps (not SMS)
Avoid:
- Text message verification (can be SIM swapped)
6. Recovery Phrase Protection (This Is Everything)
Your seed phrase is your wallet.
- Write it down physically
- Store it in 2 separate secure locations
- Never store digitally (no screenshots, no notes app, no cloud)
Optional upgrade:
- Metal backup plates (fire/water resistant)
7. Hardware + Physical Access Awareness
- Do not leave devices unlocked
- Do not connect wallets to unknown computers
- Do not approve transactions you don’t fully understand
Advanced Layer (Where This Is Going)
The system is evolving.
Security is moving toward:
- Hardware signing devices
- Multi-signature wallets
- Biometric layers
- Smart contract permissions
And eventually:
- Wallets tied to identity systems
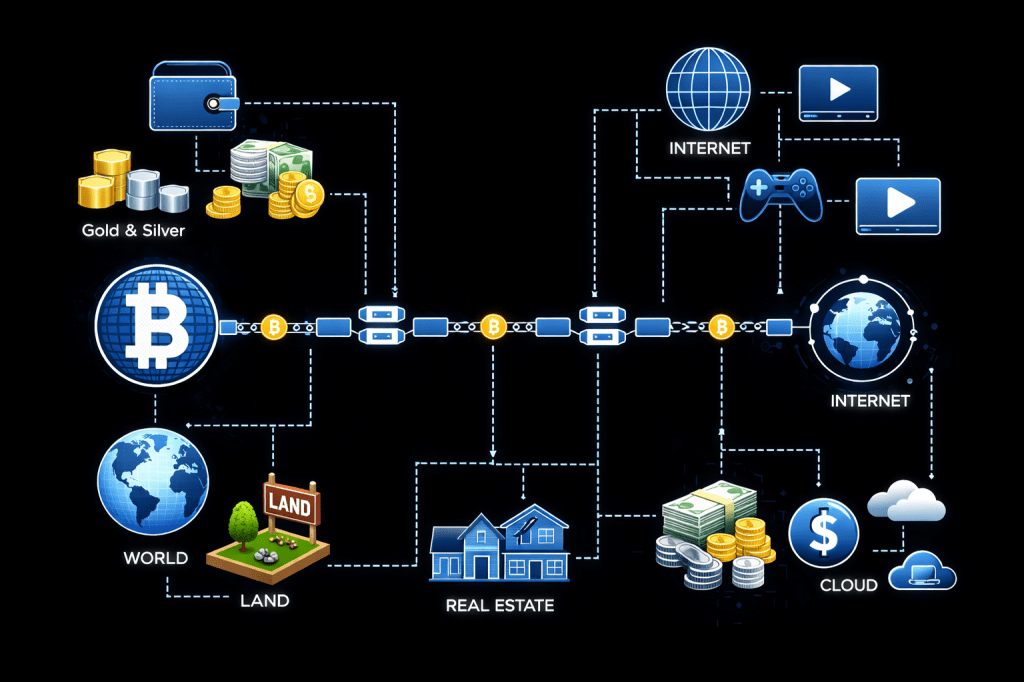
- Asset tokenization (real estate, metals, ownership rights)
This connects everything:
- Money
- Land
- Assets
- Digital systems
Exactly like the schematic you created.
The Hard Truth
Most people entering this space will lose money.
Not because the system failed—
Because they treated it casually.
This is not casual.
Closing
The wallet is not just a tool.
It is the line between:
- Participation and dependence
- Ownership and permission
- Security and loss
If you are going to step into this system, you either:
Build it correctly… or you will learn the hard way.
Discover more from
Subscribe to get the latest posts sent to your email.